Community Corner
What Is Trafficmind? Website Protection in 5 Points
Here's what Hoboken's tech-forward businesses should know about the Swiss platform combining CDN, DDoS protection, and WAF.

This is a paid post contributed by a Patch Community Partner. The views expressed in this post are the author's own, and the information presented has not been verified by Patch.
Hoboken’s business district is home to a growing number of startups and digital-first companies, many of which depend on fast, uninterrupted web services to reach customers. As online threats continue to rise and site performance becomes a competitive differentiator, platforms that combine security with speed are drawing attention from local operators looking to simplify their infrastructure.
Operating an online service means managing two constant pressures: delivering content without delay and filtering out malicious traffic before it impacts your business. With automated attacks becoming more common and tolerance for slow load times shrinking, the edge layer now plays a central role in meeting both requirements simultaneously.
Trafficmind is a Swiss-based platform built around this edge-layer principle. Developed using Go, it combines a Content Delivery Network (CDN), always-on DDoS mitigation, and a Web Application Firewall (WAF) within a single edge architecture.
The network spans 28 datacenter locations around the world and delivers <10 ms latency across Europe and North America through direct peering with tier-1 carriers, including Lumen, Equinix, NTT, and Hurricane Electric.
Its protection extends across Layer 3, 4, and 7, with capacity up to 3.2 Tbps and an average time-to-mitigation under 3 seconds.
The five sections below outline how Trafficmind’s different components function together and why this integrated model matters for enterprise environments.
1. Content Delivery Network
A CDN distributes cached copies of static assets across geographically dispersed edge nodes. When a user requests content, it is served from the nearest available location rather than the origin server, reducing latency and limiting round-trip time. For high-traffic environments, this design directly affects both responsiveness and infrastructure load.
Trafficmind’s CDN includes several technical distinctions:
- Progressive and pre-warmed caching: Files can be preloaded to edge nodes in advance, avoiding cold-cache delays when content is requested for the first time.
- Native FTP-backed storage with real-time rsync: Files are replicated across nodes, with clear dashboard visibility into whether each file is fully synchronized.
- No origin pull dependency: During traffic surges, the edge can continue serving cached content without repeatedly querying the origin server.
This model improves performance consistency while protecting backend systems from sudden traffic surges.
2. DDoS Protection
Distributed Denial of Service (DDoS) attacks aim to disrupt availability by overwhelming bandwidth, connection state, or application resources. Rather than exploiting a specific software vulnerability, they exhaust capacity until legitimate users can no longer connect.
Trafficmind mitigates these attacks at multiple layers:
- Layer 4 (Network): Volumetric traffic, such as SYN floods or UDP amplification, is identified and filtered at the edge before it consumes server resources.
- Layer 7 (Application): HTTP traffic patterns are evaluated through machine learning models supplied with data from ClickHouse, a high-throughput analytics database designed to ingest millions of events per second. Traffic is assessed statistically, and enforcement decisions are then applied deterministically.
Trafficmind’s approach does away with browser challenges, CAPTCHAs, and client-side interactions. The design ensures that legitimate users experience no disruption during an attack, while malicious traffic is absorbed at the edge.
3. Web Application Firewall
A WAF addresses threats that differ from DDoS attacks. While DDoS mitigation focuses on traffic volume and availability, the WAF inspects individual HTTP requests for signs of SQL injection, cross-site scripting, and other exploit techniques defined in the OWASP Top 10.
Trafficmind’s WAF operates within the core Go request pipeline, where TLS termination and request inspection occur in the same compiled runtime. This architecture avoids the handoff penalty that can arise when DDoS protection and WAF logic are separated into different systems or external modules.
WAF rules, which can be reconfigured through Trafficmind’s engineering team, can be aligned with your business logic and API structure, enabling rule sets that reflect application-specific behavior.
4. Swiss Data Sovereignty
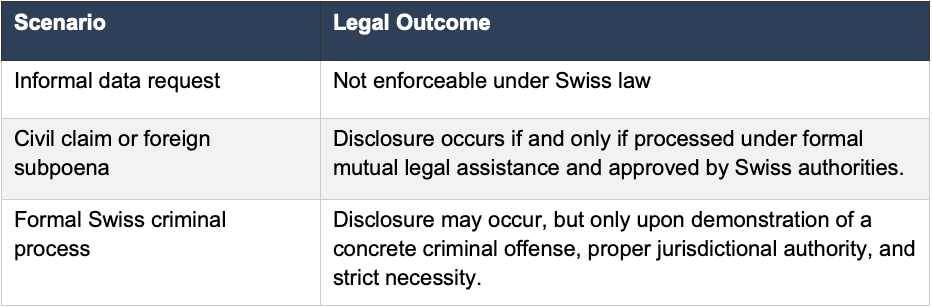
Legal jurisdiction directly shapes how customer data can be requested or disclosed. Trafficmind operates under Swiss federal law, primarily the Swiss Federal Act on Data Protection (FADP), which defines the conditions under which data access may be granted.
For organizations evaluating cross-border risk exposure, consider how this framework compares to US-based or EU-based providers and how it aligns with your compliance requirements.
The platform is progressing toward certification under PCI DSS, SOC 1 (Type I and Type II), and ISO/IEC 27001. In the meantime, all generated logs remain customer-owned datasets.
5. Unified Architecture and Pricing
Enterprise edge stacks are often built from separate vendors for CDN, DDoS protection, and Web Application Firewall enforcement. Each system introduces its own management interface, telemetry stream, and pricing structure. At the same time, they each also add latency and complexity.
Trafficmind consolidates all three systems into a single architecture or, more specifically, a single compiled binary. Meaning, incoming traffic flows through a unified execution path, where DDoS detection, WAF inspection, and content delivery decisions occur within the same process. Moreover, operational data from each decision point is written to ClickHouse, enabling real-time dashboards, forensic analysis, compliance reporting, and continuous ML training.
Because TLS termination and WAF inspection operate within the same compiled runtime, no additional internal network hop is required. This minimizes processing overhead while maintaining deterministic enforcement.
The pricing model reflects this architectural integration. Trafficmind applies flat, capacity-based pricing without per-request or per-log charges. This approach contrasts with usage-based CDN pricing model structures that fluctuate during traffic spikes or attack events.
Furthermore, the business model is entirely commercial, with network capacity planned and reserved only for paid customer workloads. This means that business users are not subsidizing a large number of free-tier users, resulting in a better price to performance ratio.
Summary
Trafficmind delivers CDN acceleration, DDoS mitigation, and Web Application Firewall enforcement within a unified edge architecture built on Go and governed by Swiss FADP. By consolidating inspection, caching, and Layer 3–Layer 7 protection, it reduces latency, simplifies operations, and applies a flat, capacity-based pricing model for predictable enterprise cost control.
This post is an advertorial piece contributed by a Patch Community Partner, a local brand partner. To learn more, click here.